It is not understandable that protocols serving huge numbers of users fall into such traps. We have previously talked about the operations of Lazarus (and its derivatives) with the promise of business or investment. These attacks have caused losses of billions of dollars so far, and in the last operation the target was Drift Protocol happened.
How was Drift hacked?
The attack, which took place on April 1, caused a cold shower for investors with the announcement that “the team is not a joke.” So how did this attack happen? multisig wallet Its use is mandatory for this type of protocol and they do this as a security measure. However, attackers can work target-oriented and reach a sufficient number of signatures to empty wallets. Currently, all protocol functions have been frozen and compromised wallets have been removed from the multisig system. The investigation is being conducted by Mandiant.
So how did such an event happen? The attackers, thought to be North Korean, started the process months ago. A big one in the fall of 2025 crypto- People who contacted the team at the conference said that they were a trading company and wanted to work together. Individuals from this group continued to meet with select Drift employees face-to-face at various major industry conferences in multiple countries over the following six months. These details are important for us to understand how serious things have become.
Attackers, who used to reach out through social media and organize artificial intelligence-supported video calls, now communicate face to face. Moreover, they are highly technically proficient and even have verifiable professional backgrounds.
After the process begins, the first meeting is organized and a Telegram group is established. What follows is months of extensive discussions about trading strategies and potential vault integrations. In today’s report, the team explains the rest as follows;
“From December 2025 to January 2026, they engaged in an Eco-system Vault on Drift, which required filling out a form with strategy details. They engaged with many contributors through many working sessions, asked detailed and insightful product questions, and invested over $1 million of their own capital. They deliberately and patiently built a functional operational presence within the Drift ecosystem.”
Integration talks continued throughout February and March 2026. Several Drift participants met again in person with individuals from this group at several major industry conferences. At this point, the relationship had been going for almost half a year. These were not strangers; They were people Drift participants had worked with and met personally.”
breaking point
Throughout this process, the attackers shared links with the team for the projects, tools and applications they claimed to have developed. It is not known exactly at what stage the team handed over the private keys to the attackers, but since file transfers and link sending occur intensively, the attackers’ job should not be difficult. In the cybersecurity world, there are concepts of FUD and binder. FUD encrypting the infected file and antivirus This is to ensure that the software is blinded to this file. It is temporary, but the encrypted file can remain camouflaged for 15 days and 1 month. If this file is uploaded to online scanning platforms, the period will be shortened (or one of dozens of antiviruses will detect it). After the file is camouflaged, it is converted to pdf or png or jpeg format with a binder. When you first look at the file, it looks like a pdf and when you click it, the pdf actually opens, but the virus also runs in the background. There are also more advanced ways to camouflage this for Word or Excel. This attack method is an average hacker The Drift example should be a warning for you as it is child’s play for many people. Attackers also apply similar methods to individual investors. Of course, these do not make the news, it is not understood how it happens, etc.
The attack path is only for the file (and this method gives full control of the device to the attackers). Apart from this, there are many methods to obtain private keys. The team thinks they were hacked in one of 3 ways.
- It may have been compromised after a team member cloned a group-shared code repository under the guise of a frontend distribution for vault.
- One of the team members was also persuaded to download a TestFlight app that the group was offering as a wallet product.
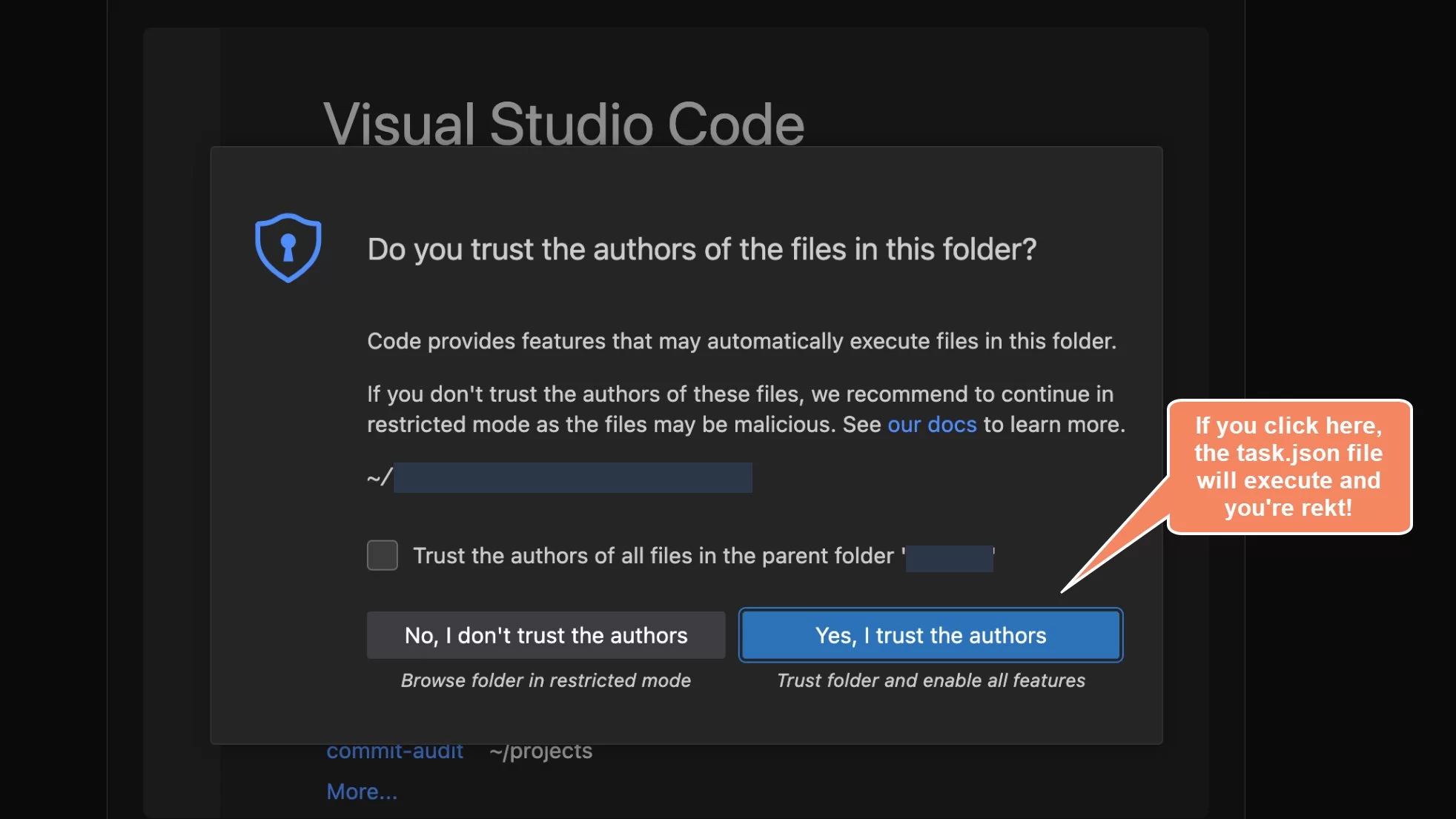
- One possibility for the repository-based vector is a known VSCode and Cursor vulnerability that the security community flagged as active from December 2025 to February 2026. Opening a file, folder, or repository in the editor was enough to silently run arbitrary code, without any prompts, flags, clicks, permission dialogs, or warnings of any kind to the user.
In other words, attackers can use 0day and make the task more complicated and incomprehensible. As a matter of fact, even though days and weeks had passed since the hacking, the Drift team realized this when the protocol was stripped.
So who did this? The case report says the following about this:
“With medium-to-high confidence supported by investigations by the SEALS 911 team, this operation is assessed by the same threat actors responsible for the October 2024 Radiant Capital attack attributed by Mandiant to UNC4736. UNC4736 is a North Korean state-affiliated group also tracked as AppleJeus or Citrine Sleet.
The basis for this connection is both onchain (the fund flows used to stage and test this operation can be traced back to the Radiant attackers) and operational (the personas recruited have identifiable overlaps with known North Korea-related activities).
It is important to note that the individuals participating in the face-to-face meeting were not North Korean citizens. North Korean threat actors operating at this level are known to use third-party intermediaries to establish face-to-face relationships.
Mandiant has not officially attributed this Drift exploit. “This decision requires the completion of ongoing device forensic examinations.”
If the team had not used isolated devices for such communications, that is, if they had opened the files sent by the attackers on a virtual server or another device, $285 million would not have been stolen today. The fact that team members do not even realize that they have been hacked, let alone being constantly suspicious and taking precautions, also calls into question the quality of team members in crypto startups. Crypto This is exactly why startups must allocate a budget for regular scanning, inspection and penetration tests.
As a result, it’s time for other protocols, even just being an investor is not enough to get rid of it. “It’s your turn.” That’s why you have to choose between taking the necessary precautions and getting hacked.









