Google has been working towards a responsible transition to post-quantum cryptography since 2016, and now is the time for a warning. published article. Discussions were intense in the cryptocurrency community today, as the article dated March 31 included details that cryptocurrencies, especially Bitcoin’s encryption standard, may also be at risk. So what’s the real deal?
What is Quantum?
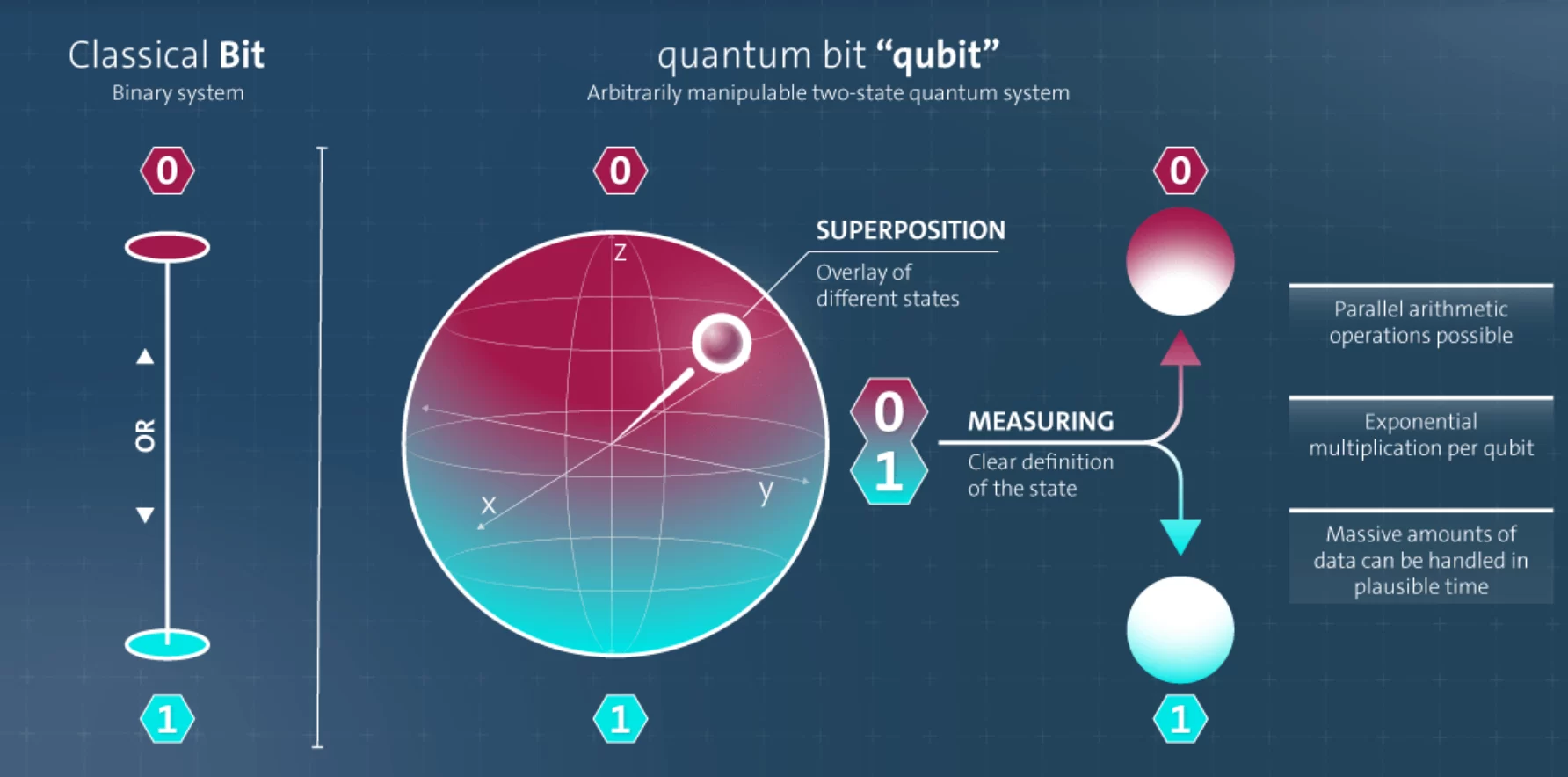
First, let’s start with what it is. The computers and systems we know work with 0 and 1. This is a basic knowledge that most of you learned at school. Quantum Computers use the principle called “Superposition”, which means that both 0 and 1 can be present at the same time. Classical computers needed more time than the age of the earth to decipher Bitcoin’s encryption algorithm. In the past, scientists calculated that 20 million physical qubits (quantum bits) were required to crack this password.
Developing and even rapidly developing technology now reduces this time to reasonable levels. In other words, Bitcoin’s encryption algorithm is moving “towards the decipherable phase”. Google’s new paper reduced this need to less than 500,000 qubits by improving “error correction” techniques. In the future, this will decrease even more with developing algorithms and hardware. This is just like the change in this process between trying to write your hardware store’s inventory in the contact section of the fax machine and printing a report and trying to get a stock report, and today you can easily print it from the printer. When you had a fax machine, printing an inventory report was possible with the method you developed after a long effort, but then printers came along and everyone could do it much more smoothly. Google is now warning that it may soon be possible to print inventory from a fax machine, meaning that our technology is approaching this stage.
In the next stage just Google Not just more companies, countries, and then smaller companies and eventually individuals will have these capabilities.
Google’s Warning
Google issued a warning on March 31 about the current and future state of the technology, saying, “We are moving this technology forward and we do not want to have the power to open all the locks at once and face serious consequences.”
“We show that future quantum computers may be able to break the elliptic curve cryptography that protects cryptocurrencies and other systems, using fewer quantum bits and gates than previously thought. We want to raise awareness of this issue and offer recommendations to the cryptocurrency community to increase security and stability before this happens.” – Google
Google has urged cryptocurrency teams and others to transition to post-quantum cryptography (PQC), which is resistant to quantum attacks.
“We have collaborated with the US government to share this research responsibly and developed a new method for disclosing these vulnerabilities through zero-knowledge proof, making it possible to verify these vulnerabilities without providing a road map to malicious actors. We urge other research teams to do the same to keep people safe. We look forward to continuing our work in the industry, along with other organizations working on responsible approaches, such as Coinbase, the Stanford Blockchain Research Institute, and the Ethereum Foundation, in line with our 2029 timeline.”
The company made the above statement regarding the process in which crypto actors such as the Ethereum Foundation were involved. So the cryptocurrencies have not been decrypted and Google will not put dormant Bitcoins into circulation, but the technology is moving towards this stage (as there has already been a nearly 20-fold reduction in the number of physical quantum bits required to decrypt ECDLP-256) and it is time for the crypto giants to take precautions against crypto risk. Google gives the world time until 2029.
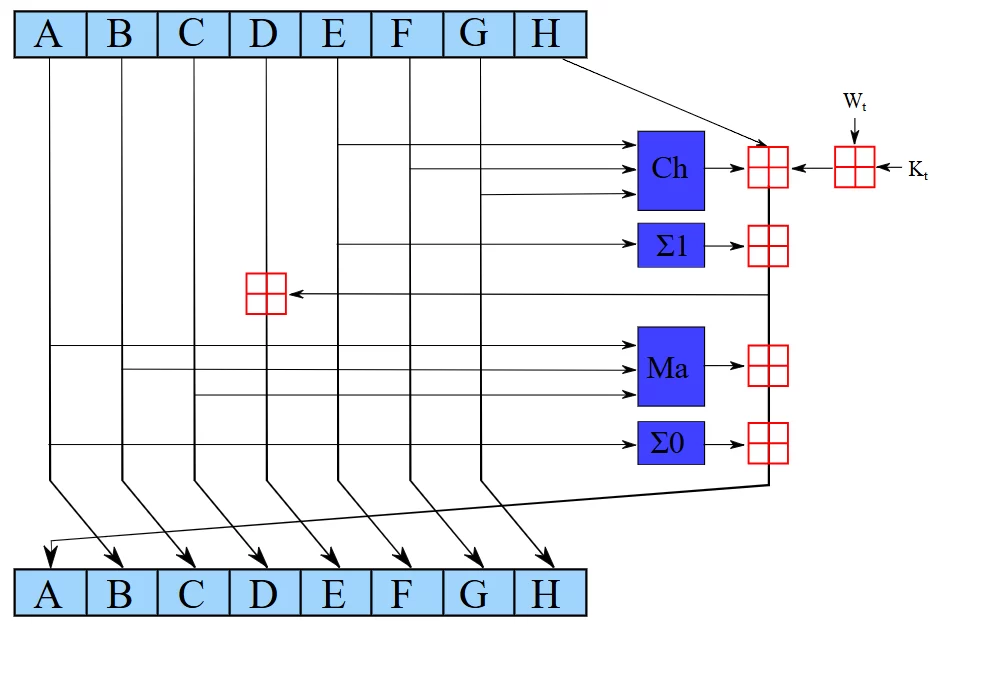
“Governments and other organizations, including Google, have been preparing for this security challenge for years. With continued scientific and technological advances, CRQCs are moving closer to reality, necessitating a transition to PQC, which is why we recently announced our 2029 transition timeline. In our white paper, we describe the quantum computing “resources” (i.e., quantum bits and We express our resource estimates in terms of the number of logical quantum bits (error-corrected quantum bits made up of hundreds of physical quantum bits) and Toffoli gates (expensive elementary operations on quantum bits, which are the primary driver of the time required to execute many algorithms).
Doomsday Scenario?
Let’s simplify. Quantum computing is advancing to the point where it can break SHA-256. It is the basis for everything in this world, from digital signatures to military secure communications, from payment encryption on e-commerce platforms to much more. In other words, when SHA-256 is “cracked” (huge computing power is required to break it. Google can do this for the USA and it is not likely to have many competitors at this stage). Before Bitcoin, the USA can seize all the confidential data of the states it sees as enemies, secure the banking infrastructure in the country, and then circulate the assets in Nakamoto’s wallet for pleasure. So, there is a lot to do until Bitcoin’s turn comes.
In other words, Google is not trying to make encryption algorithms breakable by sitting down and saying “Let’s break Bitcoin’s password (!).”
What is SHA-256?
SHA-256 (Secure Hash Algorithm 256-bit) converts any data into a unique string of 64 characters, that is, it is a one-way algorithm. Where is it used? When you access a website (HTTPS), your browser checks whether the site’s certificate is genuine. SHA-256 signatures are used to verify that these certificates have not been corrupted.
When you become a member of a site, your password is hashed with SHA-256 (usually with the addition of “salt”) and saved in the database. In digital signing of official documents, the content of the document is hashed with SHA-256 and then encrypted with the sender’s private key.
Anti-virus software has a huge database of SHA-256 digests of known viruses.
Dropbox or Google Services like Drive avoid storing thousands of copies of the same file. SHA-256 uses. When downloading libraries for Linux or programming languages, a SHA-256 check is performed to verify that the downloaded packages are the same as on the server. This prevents “man-in-the-middle” attacks.
When your computer boots up, it checks the motherboard (UEFI) SHA-256 signatures to check whether the operating system (Windows/Linux) kernel is genuine. When smart home devices or industrial sensors receive a software update over the internet, they verify with SHA-256 that the update file comes from the manufacturer. Police or cybersecurity experts obtain the SHA-256 digest of the file and seal it to prove that the image (copy) they receive from a computer at the scene of a crime has not been changed during the court process.
DNS records are protected with SHA-256-based digital signatures to prevent internet addresses (like googlecom) from redirecting you to a wrong IP address. Digital signatures created with SHA-256 are added to email headers to prove that the emails you send have not been modified in transit and actually originate from your server.
The list goes on, so if we see Quantum break it at some point, if the entire internet encryption infrastructure is not upgraded to the required level that day, the problem will not only be a problem of cryptocurrencies.
Latest: Will BTC and ETH Come Out of This War?
Ethereum the team is already quantum risks He took action for precautions and added it to his road map. Before 2029, Ethereum will easily insure itself against risks. The situation is slightly different for Bitcoin because the principle of immutability is slightly misinterpreted here. Even for security, we can see discussions in the Bitcoin community throughout the process. We have all seen what kind of discussions and risks posed by Taproot or ordinals.
In any case, the Bitcoin community will not resist this update in order to keep Bitcoin alive, so BTC and ETH will easily come out of this quantum war, but the time has come for them to determine their road map and take action. There is SHA256, there is SHA512, there are more advanced versions, and making encryption algorithms resilient is a much simpler thing than developing quantum computing systems. In summary, you can breathe easy.












