cryptocurrency Telegram is one of the applications used extensively by investors and a significant vulnerability has been detected. 0day vulnerabilities are still active vulnerabilities that application developers have not fixed. The score of the last detected vulnerability is quite high, so you need to pay attention.
Telegram 0day Vulnerability March 27
Telegram A new vulnerability coded ZDI-CAN-30207 has been detected for This vulnerability was included in the Zero Day Initiative’s vulnerability list with a CVSS score of 9.8 out of 10. You can actually see this score as the magnitude of an earthquake, and vulnerabilities with scores above 8-9 mean that attackers gain high-level privileges in the application.
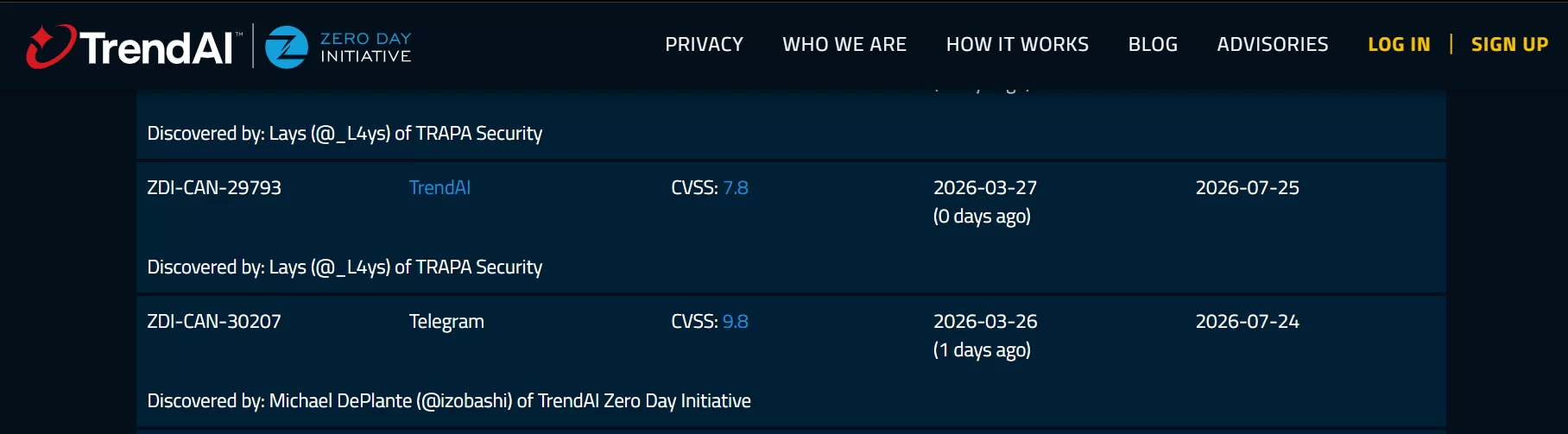
This vulnerability was reported on March 26 and will be published if the vulnerability is not closed by July 24. The technical details and mechanics of the vulnerability are unclear because those who detect it do not share this information before the vulnerability is patched. The main problem is that this vulnerability, detected by relatively well-intentioned (white, gray hat) hackers, has the potential to be detected by malicious attackers in the coming hours.
It is thought that the detected 0day vulnerability allows a low-complexity remote attack that can be carried out without requiring privileges or user interaction. Telegram has not yet made a statement on this issue.
Precautions to be taken
All Telegram We are talking about a vulnerability that concerns users because a vulnerability has been detected that has a very high score and that attackers can harm you even if you do not make a mistake. When it comes to a 0-day exploit with such a high score (9.8 CVSS) for Telegram (or any messaging app), the biggest risk is zero-click attacks. Although technical details are still kept secret, such exploits are usually triggered during background processing of media files or links.
- First, follow Settings > Data and Storage. Turn all options (Cellular Data, Wi-Fi, Roaming) under the Automatic Media Download heading to “Off”. In this way, a file sent to you will not be downloaded to your device unless you tap on it and say “Download”.
- Some severe exploits can be triggered by simply sending a call signal (even if you don’t pick it up). Go to Settings > Privacy & Security > Calls. “Who can call me?” Update the option to My Contacts or Nobody. Prevent your IP address from being seen directly by setting the “Peer-to-Peer” feature to “My Contacts” or “Nobody”.
- In order to carry out mass attacks, attackers can add you to groups you do not know through bots and share malicious files in these groups. “Who can add me?” in Settings > Privacy and Security > Groups and Channels tab. Change the setting to My Contacts.
Although there is until July 24, 2026, Telegram can release a “silent patch” at any time. Check for Telegram updates daily on the App Store or Google Play Store. Since there is a risk that different attackers may detect the vulnerability (they may have detected it even now), install the patch immediately when it arrives. Especially stay away from links that look like “tme/proxy” but contain another link underneath.